Researchers observed Iran-linked actors targeting IP cameras across Israel and Gulf countries, likely to support military intelligence and battle damage assessment. According to the Check...
In this post, I will talk about how AI-Driven governance is changing enterprise cybersecurity. Cybersecurity has traditionally focused on protecting networks from unauthorized access. Organizations...
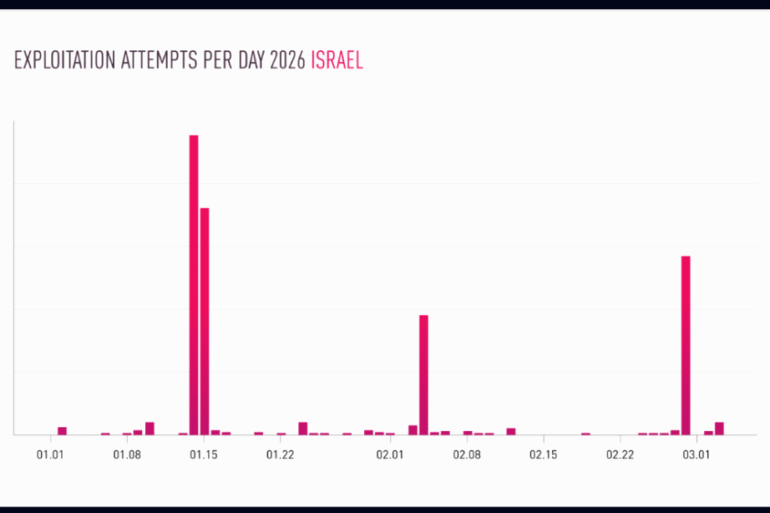
Cisco warns that two recently patched Catalyst SD-WAN flaws, CVE-2026-20128 and CVE-2026-20122, are already being actively exploited in the wild. Cisco warned customers that threat...
U.S. Cybersecurity and Infrastructure Security Agency (CISA) adds Apple, Rockwell, and Hikvision flaws to its Known Exploited Vulnerabilities catalog. The U.S. Cybersecurity and Infrastructure Security Agency...
In this post, I will show you why CRM data protection should be a priority for growing businesses. Your customer relationship management (CRM) system is...
In this post, you will learn why we make bad security decisions when the stakes are high. Even the most seasoned professionals can falter when...
In the latest development, the multichain trader’s missing tool is here and Banana Gun built it. There is a specific frustration that every serious on-chain...
In this post, I will talk about the best Pollo AI alternative in 2026. When most people compare AI tools, they look at features. When...
StealC V2 spread via malicious Blender files on 3D model sites like CGTrader, abusing Blender’s ability to run hidden Python scripts. Cybersecurity firm Morphisec reported that...
I hate hyperbolic news headlines about data breaches, but for the “2 Billion Email Addresses” headline to be hyperbolic, it’d need to be exaggerated or...
The Invisible Threat: Reimagining Third-Party Risk Management Cybersecurity leaders are drowning in questionnaires while threat actors are swimming in data. The traditional approach to vendor...
Multiple popular npm packages were compromised in a supply chain attack after a maintainer fell for a phishing email targeting 2FA credentials. A supply chain...