In this post, I will show you how online casinos became a prime target for credential stuffing and account takeover attacks. Online casinos are everywhere...
Discover the most secure sweepstakes gaming platforms. Learn how fair play technology and encrypted social casino platforms protect your virtual currency entertainment. The digital entertainment...
Phishing remains one of the most effective tools in the cybercriminal arsenal, especially when threat actors abuse the credibility of trusted institutions and familiar digital...
Discover how company liquidators manage insolvent winding-up processes effectively. Our blog explains the essential steps and strategies involved. Key Highlights Company liquidators are appointed to...
Discover how Construction Safety Compliance Software: Keep Your Site Safe and Audit‑Ready Every Day can enhance safety and streamline your site’s compliance. Key Highlights Embrace...
In this tactical blueprint tutorial post, I will talk about the operational standards for modern close protection. In the current global security landscape, the shift...
The Dutch Ministry of Finance took treasury banking portal offline after a cyberattack; core tax systems were not affected. The Dutch Ministry of Finance took...
The U.S. Cybersecurity and Infrastructure Security Agency (CISA) adds a flaw in Citrix NetScaler to its Known Exploited Vulnerabilities catalog. The U.S. Cybersecurity and Infrastructure...
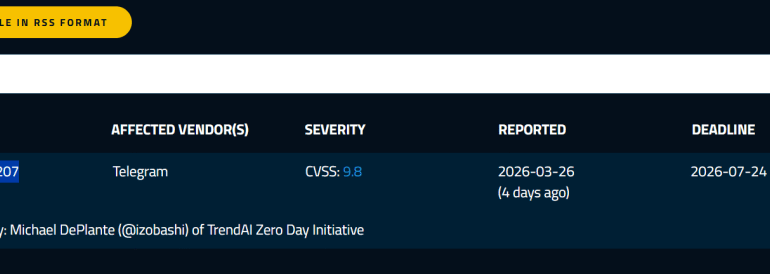
A critical Telegram flaw could allow zero-click remote code execution on devices, but Telegram denies it. Researcher Michael DePlante (@izobashi) of TrendAI Zero Day disclosed...
In the latest development, Banana Gun now facilitates one Google login, five blockchains, zero seed phrases for crypto trading. Ask someone why they have not...
Dimitris Georgiou has been a self-professed computer geek since the early 80s. At university, he studied the convergence of educational technology with computer science as...
In the latest development, Dubai residential security installations double as prices fall and communities expand. Dubai, UAE. The residential security market in Dubai reached AED...