Preparing and Staying Safe During Civil Unrest The growing number of incidents...
In this post, I will give you hot tips for finding the...
A new round of the weekly Security Affairs newsletter has arrived! Every...
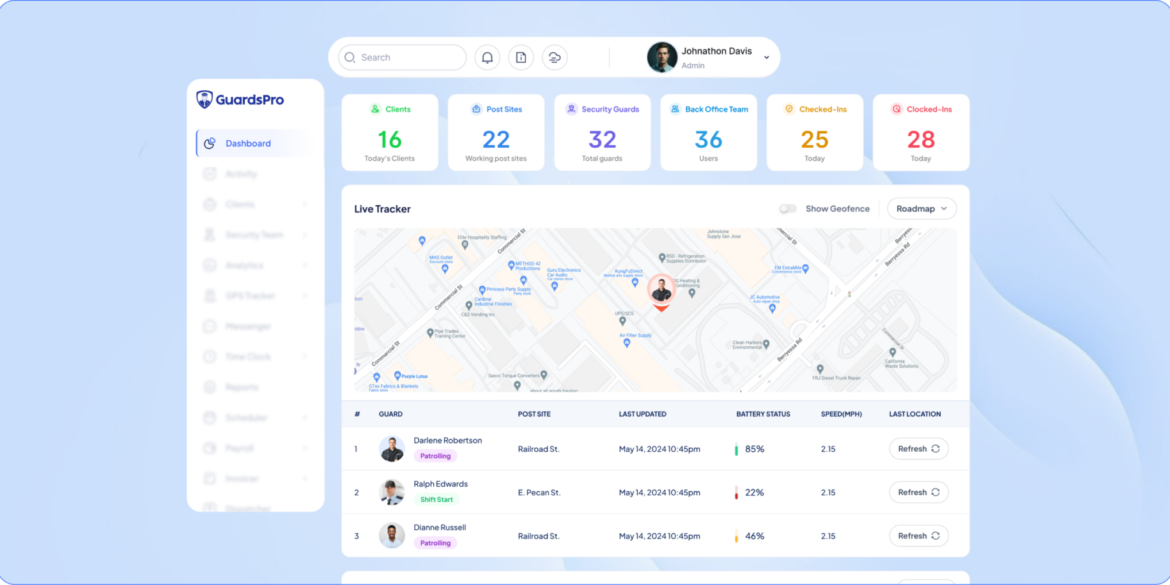
In this post, I will show how to choose the best security...
Key Takeaways Armed security guards and law enforcement operate as a coordinated...
INTERPOL dismantled 45,000 malicious IPs and servers and arrested 94 suspects in...
U.S. Cybersecurity and Infrastructure Security Agency (CISA) adds Google Chrome flaws to...
Explore how to build a low-overhead Micro-SaaS startup in Romania. Learn about...
In security operations, decisions often need to be made in real time....
In this post, I will talk about why permission set complexity in...
Chrome zero-days continue to pose a major risk for cyber defenders. Earlier...
In this post, I will talk about the future of custom software...