Learn how Checkmarx and AWS have partnered to help your financial services...
Administrator Pekoske and other TSA leaders met with innovation partners to explore...
General Dynamics Information Technology (GDIT) has welcomed Patrick Flynn as the new...
On April 18, 2024, the Committee on Homeland Security convened to scrutinize...
Discover your exposure to the XZ Utilities backdoor in 10 seconds or...
In their haste to deploy LLM tools, organizations may overlook crucial security...
Did you know that the total number of data breaches more than...
Professionals in any profession need to train. The more training you do,...
OWASP chapters and members gain Codebashing access to boost adoption of application...
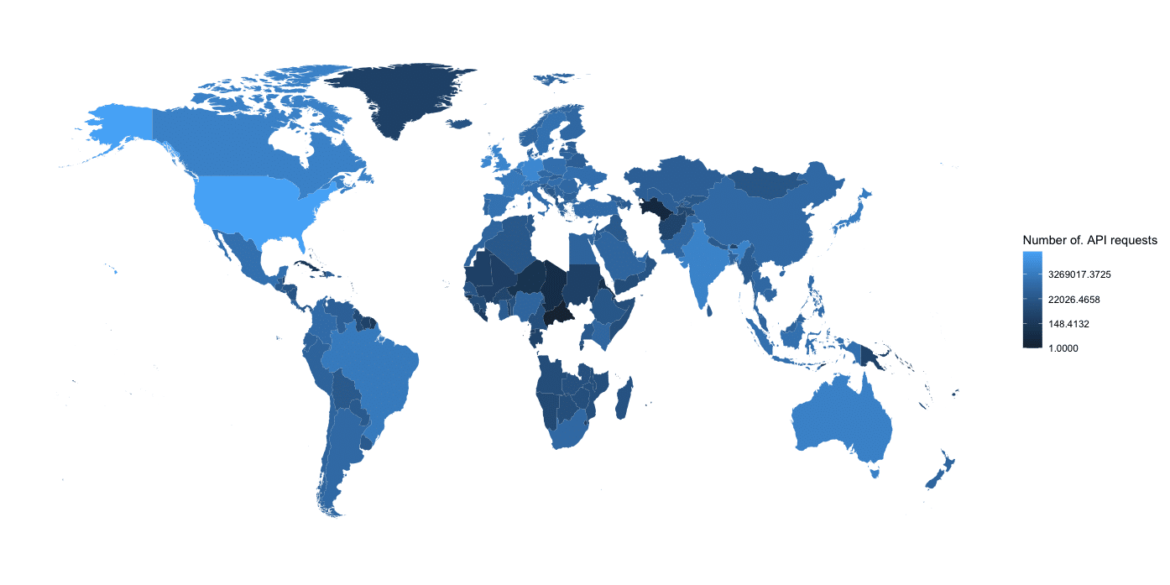
API Security: What Every Developer Needs to Know At Traceable, we monitor...
In this blog, we will dive into an interesting method for intercepting...
Imagine yourself standing in a local fair at night. The bright lights...