After the XZ Utils discovery, people have been examining other open-source projects....
In introducing their Defense Quantum Acceleration Act last week, U.S. Sen. Marsha...
The U.S. Department of Homeland Security released a notice of funding opportunity...
The U.S. Department of Homeland Security (DHS) recently announced more than $1.8...
This week, a collection of Republican and Democratic legislators introduced a bill...
Our True Business | Synopsys opsdemon Mon, 15/04/2024 – 09:00 We’re in...
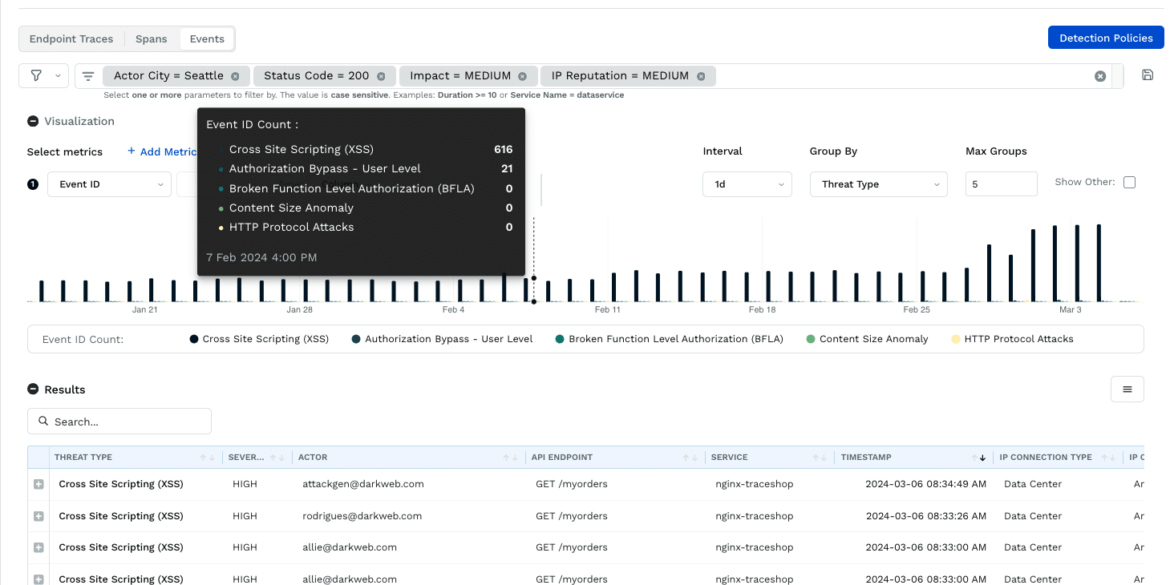
Traceable API Security Platform Updates – February 2024 February’s releases include analytics...
This article is based on the Elephant in AppSec podcast episode with...
Industrial control systems, application containers, and mobile devices are the top contenders...
Traditional security practices, often siloed and reactive, struggle to keep pace with...
A surge of confidence by supporters of the Islamic State terror group...
An Afghan migrant on the terrorist watchlist spent nearly a year inside...