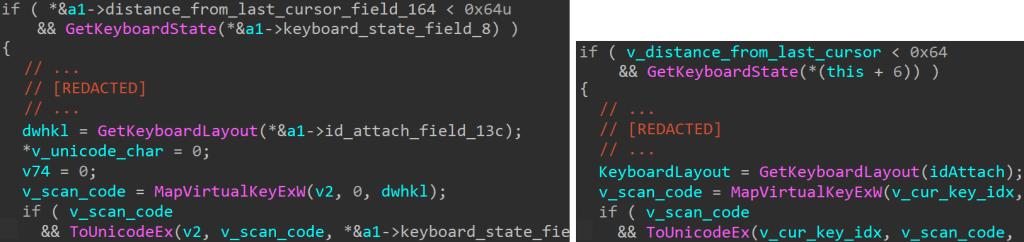
APT28 used BEARDSHELL and COVENANT malware to spy on Ukrainian military personnel,...
Learn how proxy purchase online works, how to purchase proxy servers safely,...
In this post, I will talk about how to safely store seasonal...
In this post, I will talk about the role of backup power...
U.S. Cybersecurity and Infrastructure Security Agency (CISA) adds EPM, SolarWinds, and Omnissa...
In this post, I will show you how to streamline incident response...
Ericsson US reports a data breach after attackers hacked a service provider,...
The phone rings at 2:00 AM. A cannabis dispensary in West Hollywood...
In this post, I will answer the question – is it safe...
In this post, I will talk about why top retailers switch to...
In this post, I will talk about the secure cloud storage for...
In this post, I will talk about the true cost of free...